NETWORK TAPS
See All Your Network Traffic. All the Time.
Identify traffic bottlenecks and spot threats without compromising network performance.

Providing Total Network Visibility For
Ethernet TAPs
Monitor your network in real time without the risk of downtime. Heartbeat technology ensures critical traffic flows even when monitoring tools fail.
-
Suitable for copper connections
-
Automatic bypass if tools go offline
-
Flexible deployment options


Passive Fiber TAPs
Improve network monitoring with our always-on Passive Fiber Optical TAPs. Simultaneously capturing sent and received data, our TAPs provide total visibility, even in the event of an electricity outage.
- No configuration needed
- Zero latency
- Real-time monitoring up to 400Gbps speeds
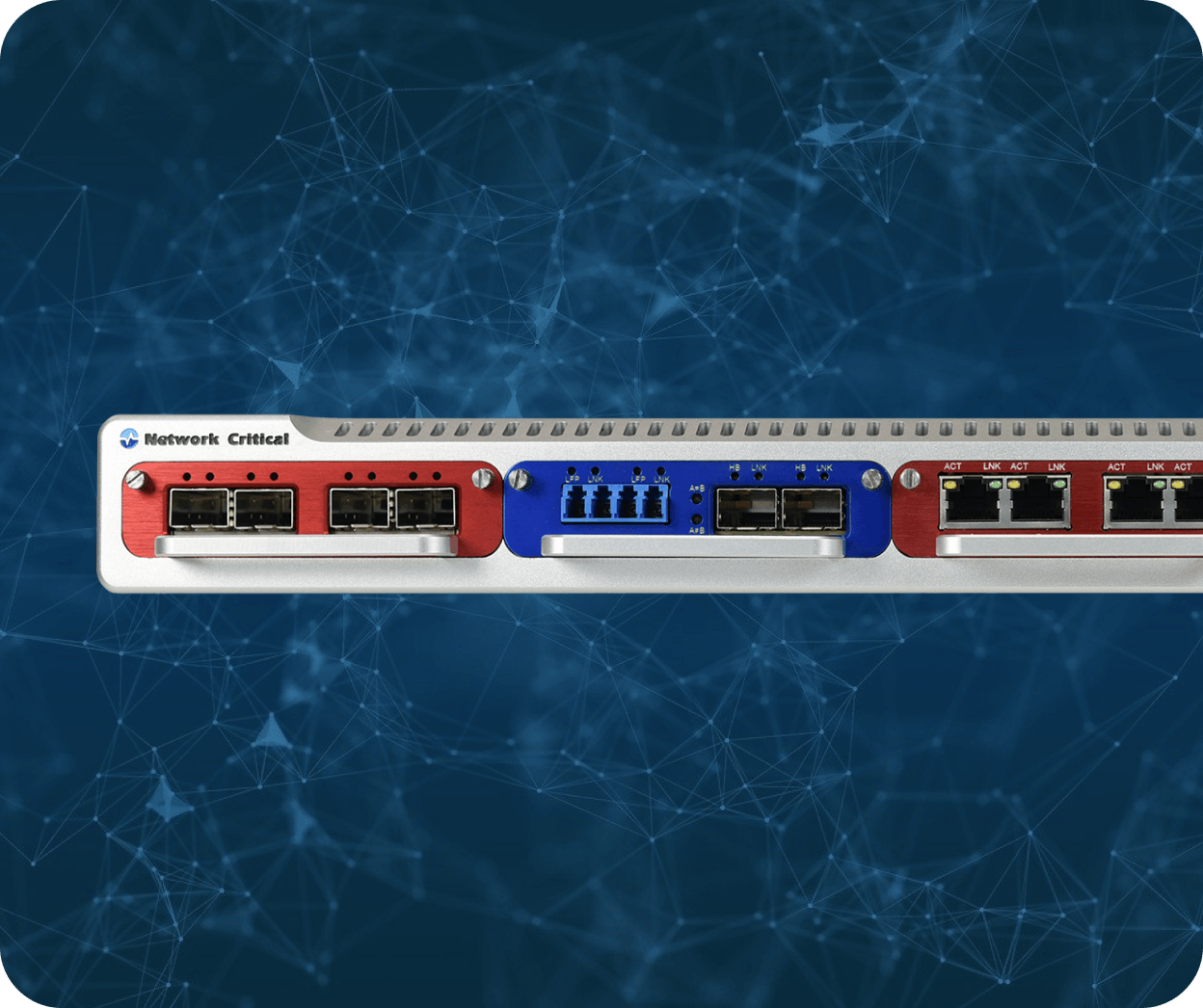
ByPass TAPS
The SmartNA-XL™ bypass TAPs detects when inline security tools fail and redirects traffic in real-time.
- Dual hot-swappable power supplies
- Modular chassis supporting 1G, 10G, and 40G
- Flexible deployment options
Get the Full Picture of Your Network With
- 100% Traffic Capture
- Retrieve every byte of network traffic data – never let a threat go unnoticed.
- Zero Impact
- Monitor your network without any risk to performance or reliability.
- The Industry Choice
- 90% of companies in high-compliance industries prefer TAPs to SPAN.
- Lower Costs
- Reduce troubleshooting time and operational costs by up to 50%.
What Our Customers Say
“Developing and managing key performance indicators is all about accuracy of information. The Network Critical products provide 100% accurate traffic visibility on the key links, which is vital for us.”
Vodafone
Network Performance Monitoring Engineer
“Unauthorized manipulation of our monitoring systems can have serious safety and production consequences. Network Critical TAP’s help us manage security without impacting network traffic.”
BP
Director, IT Services
“I’m delighted to say the use of Network Critical’s TAPs across the multiple rigs, has helped us complete all our first flight test objectives on schedule, whilst at the same time offering the additional capability to resolve some of the inherent limitations of layer 2 switches.”

Airbus
System Test Lead Engineer
Proud to Partner With
Find Network Solutions That Work for You
Product
SmartNA
SmartNA-XL
SmartNA
SmartNA-XL
Height in Rack Units (RU)
1-2RU
1RU
Width
19”
19”
AC Redundant Power Supply (Hot Swappable)
DC Redundant Power Supply (Hot Swappable)
Hot Swappable Cooling Fans
SmartNA
SmartNA-XL
Maximum Visibility (Bi-directional)
1,700Mbps
480Gbps
SmartNA
SmartNA-XL
Physical Interfaces
17
2 x QSFP / 20 x SFP+
(Numbers show maximum physical interface, but these cannot be used all together at once.)
Max. Number of 1GB Ports
17
20
Max. Number of 10GB Ports
20
Max. Number of 40GB Ports
2
SmartNA
SmartNA-XL
10/100/1000BASE-T Copper Port
1Gb SFP Port
10Gb SFP+ Port
25Gb SFP28 Port
40Gb QSFP+ Port
10/100/1000BASE-T Copper TAP
1Gb/10Gb Fiber TAP
SmartNA
SmartNA-XL
1G Optical
1G Bypass Copper
1G Bypass Optical
10G Bypass Optical (This is with the 10G V-Line Module)
SmartNA
SmartNA-XL
10/100/1000BASE-T CopperPhysical Bypass Protection
1Gb Fiber Active BypassProtection
10Gb Fiber Active BypassProtection (Also available in 40G and 100G)
User Defined Bit-level Filtering
Traffic Aggregation
Traffic Distribution
FCC/CE Certified
SmartNA
SmartNA-XL
Layer 2-4 Packet Filtering
Application Session Filtering
Persistent Load Balancing
Static Load Balancing
Header Stripping
Tunneling/De-Tunneling
Packet Slicing
Payload Masking
Source Port Labeling
SmartNA
SmartNA-XL
RESTful API
Role Based User Accounts
Multiple Levels of User Account
SNMP Traps
Event Monitoring and Alarm
Generation
Link Status Trap
Traffic Statistic/Counter in Each Port
WebUI (HTML5) for System Access
CLI Configuration and Management
GUI Configuration and Management
SNMP v2c & 3 Support
Authentication & Authorisation TACACS+
FAQS
-
A network TAP creates an exact copy of all data flowing between two points in your network. It does
this without interrupting or changing any of the live traffic. Think of it like a rear-view mirror for your
network always giving you full visibility. Network Critical TAPs ensure you capture 100% of the data,
every time. -
TAPs are used to monitor network traffic for performance, security, or compliance. They give tools
like firewalls, intrusion detection systems, or network analysers a clean, reliable copy of your data to
work with without ever interfering with your actual traffic. -
It usually refers to a hybrid device that combines the traffic-copying function of a TAP with some
switching or filtering features. At Network Critical, we offer platforms like the SmartNA-PortPlus that
do exactly that: TAP, filter, and route traffic all in one.
-
High quality TAPs are built to be ultra-reliable and fail-safe, especially in critical environments where
downtime isn’t an option. Network Critical TAPs are engineered to handle high speeds and work
flawlessly 24/7, so while they’re an investment, they save time, money, and outages in the long run. -
Port mirroring (SPAN) uses a switch to copy traffic, but under heavy load, it can drop packets or miss
data. TAPs don’t have this problem. They give you a complete, lossless copy of all traffic. If full
visibility matters to you, TAPs are the better choice.
What is a Network TAP?
A Comprehensive Guide to Network Visibility





